For many organisations, cloud adoption is no longer a question of if, but how much. This is a trend internationally that cloud becomes a 'must-have' and it is also happening in Singapore. According to the 2015 (ISC)² Global Information Security Workforce Study (GISWS) - a study of nearly 14,000 information security professionals worldwide - respondents globally have made cloud a priority for their organisations and will further do so over the next two years.
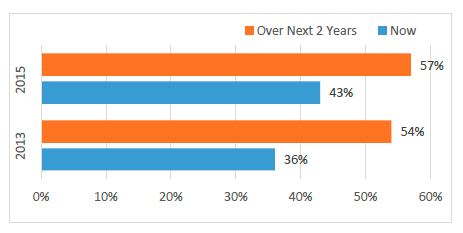
Cloud Computing Priority 2013 vs. 2015 (Percent of Global Survey Respondents Choosing Top or High Priority)
Source: 2015 (ISC)² Global Information Security Workforce Study - by Frost & Sullivan
According to the 2015 Cloud Security Spotlight Report - a survey of over 1,000 cybersecurity professionals - cloud computing is delivering on the hype in terms of flexibility, availability and cost reductions. However, security and compliance remain the biggest concerns. Security is still the biggest perceived barrier to further cloud adoption, and nine out of ten organisations are very or moderately concerned about public cloud security.
Despite the concerns, organisations are beginning to deploy cloud anyway. Detailing the prevalence of various cloud models, the 2015 (ISC)² GISWS found that 44% of the global respondents report cloud is primarily used for Software as a Service (SaaS), followed by Infrastructure as a Service (IaaS) (32%), and the least common is Platform as a Service (PaaS) (24%). While the Singapore data is quite consistent with global trends, 39% of those respondents reported that cloud is primarily used for SaaS; followed by IaaS (36%) and the least is PaaS at 25%.
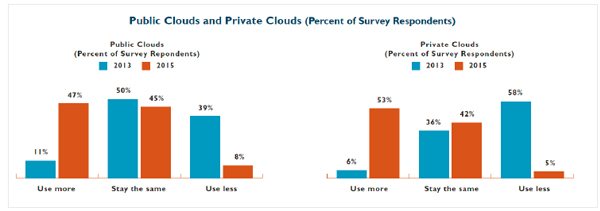
Public Clouds and Private Clouds (Percent of Global Survey Respondents)
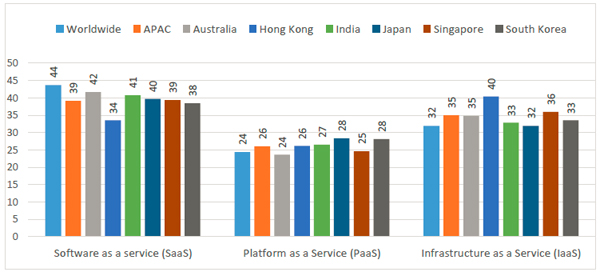
Cloud Usage (Average in %)
Source: 2015 (ISC)² Global Information Security Workforce Study
Placed into the context of the Cloud Security Alliance's "Notorious 9 Security Threats", Singaporean respondents indicated their level of concern for each threat is a bit higher than worldwide and APAC respondents except for 'Account Hijacking' and 'Denial of Service'. 'Data breaches' and 'Data loss' topped the list of Singaporean respondents' concerns.
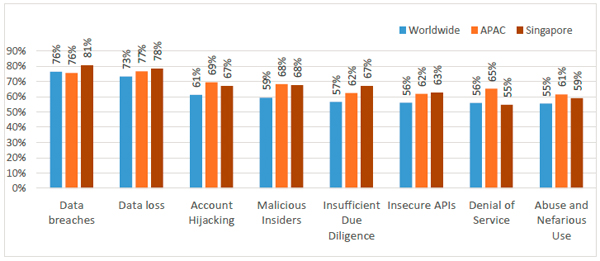
Cloud Security Alliance's Cloud Security Threats (Top/High Concern)
Source: 2015 (ISC)² Global Information Security Workforce Study
So what methods should information security professionals employ to offer the greatest chance of elevating cloud assurance? From these findings, the largest proportion of information security professionals believe that data encryption (18% of global respondents) is the surest path to elevating cloud assurance. The second and third methods include continuous monitoring (11% of global respondents) and incorporating security into design and implementation (9% of global respondents) respectively. Singaporean respondents are offering different views: They see adopting security governance as a way of elevating information assurance in the cloud. Although they also rank data encryption as the highest, the second most popular method that they trust is adopting security governance, which Singaporeans rank higher than their counterparts worldwide and in the APAC region. Security policy is not about the technical aspects of information security. It is all about defining responsibilityand accountability, and structuring policies to ensure that decisions are made in such a way that they help an organisation achieve an accepted level of risk.
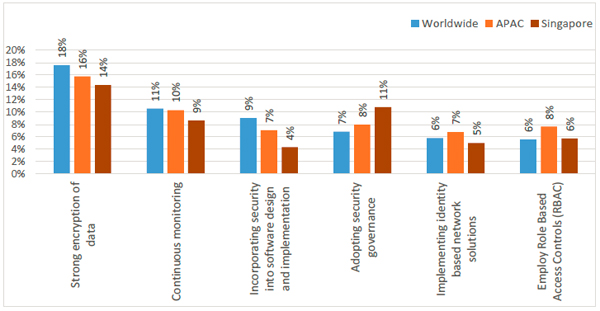
Elevating Cloud Assurance
Source: 2015 (ISC)² Global Information Security Workforce Study
In addition to the model and cloud assurance consideration aspects, when organisations consider cloud adoption, the people aspect should be a crucial component of the evaluation and ultimate decision making processes.
Having qualified people lead a thorough evaluation process can help organisations responsibly take advantage of cloud services. IT professionals who understand how cloud services can be securely implemented and managed within their organisation's IT strategy and governance requirements are essential. In a bit of dichotomy, cloud adoption relieves in-house security professionals of certain security operations that are entrusted to the cloud providers, but lingering concerns about security in cloud environments contribute to the need for in-house security professionals to invest in cloud security education and training, and be active in managing security and compliance in cloud environments. In the APAC region, including Singapore, cloud computing is also the area requiring the most training and education as acceptance of the use of cloud continues to grow.
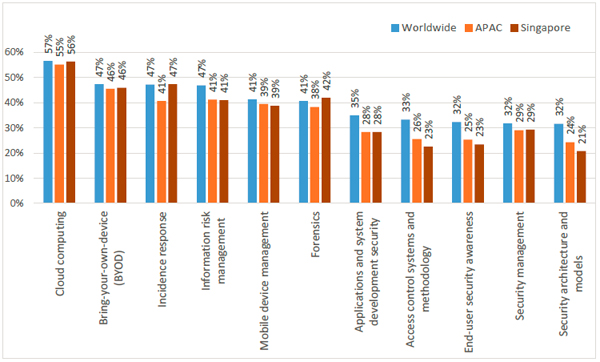
Demand for Training and Education
Source: 2015 (ISC)² Global Information Security Workforce Study
As powerful as cloud computing is for the organisation, understanding its information security risks and mitigation strategies is critical. Legacy approaches are inadequate, and organisations need competent, experienced professionals equipped with the right cloud security knowledge and skills to be successful. Certification provides assurance to cloud service customers that their critical security requirements are being met. Therefore, it is the best policy that cloud service customers identify the well-established security certifications that are important to their organisations and insist their cloud service providers demonstrate their conformance to international standards.
As the official training partner of (ISC)², we are currently offering three certification courses from (ISC)2
- NICF - Certified Information Systems Security Professional (CISSP®) CBK® Review Seminar, NICF - Certified Secure Software Lifecycle Professional (CSSLP®) CBK® Education Program, and Certified Cloud Security Professional (CCSP) CBK® Training Seminar.
Chuan-Wei Hoo is an adjunct staff at NUS-ISS teaching NICF - Certified Information Systems Security Professional (CISSP®) CBK® Review Seminar.